A Cybersecurity Guide for the Holidays

The summer vacation season is a time for carefree fun and relaxation. That’s when we look for the perfect getaway—a wonderful hotel with a pool or a cozy cabin in the mountains. We browse through hundreds of offers from travel agencies, flights, trains, and so on. It’s also a time when cybercriminals don’t take a vacation and become more active. Why? We let our guard down and get excited about a great deal we’ve found. That’s the moment when we become less attentive and more susceptible to all kinds of manipulation, known as phishing.
What could go wrong? From credit card theft and money being withdrawn from your account to losing access to all your online accounts. Your vacation adventure could turn into more than just a digital nightmare.
See what you can do better and how to prepare for a great vacation.
Table of Contents
Secure reservations
Most trips start with finding the perfect place to stay, followed by booking it through popular online platforms. These platforms often attract users with attractive prices, the ability to change or cancel a reservation, and, above all, allow users to read reviews about a particular place and compare it with other similar accommodations.
The process seems simple. You create an account on one of these websites, search for a hotel, click “Book,” and then make the payment. However, all it takes is a moment of inattention or haste, and instead of paying for your reservation, you end up transferring money to a cybercriminal.
How can you avoid this, and what should you look out for?
First and foremost, secure your account on such a website with a strong password. This is a fundamental rule for using online services, and you should follow it every time you create a new account anywhere. Whenever possible, be sure to use two-factor authentication.
When planning a trip or making a reservation, it’s worth keeping the following in mind:
- Are you sure the website you’re on is the official website of the venue or a search engine for such places? Make sure there are no typos in the URL, such as “boooking.com” instead of “booking.com”;
- Check whether the contact information listed on the website for that property can be found on other websites offering accommodations;
- Simply checking whether you can call that location is also a good idea;
- Make sure the website offers various payment methods, such as payment upon arrival, advance payment, or cash payment. Cybercriminals typically only offer electronic payments—usually through a platform other than the one where you were searching for accommodation;
- If a website suggests contacting you via messaging apps like WhatsApp or Telegram rather than the portal’s built-in chat feature, do not agree to this, as it is most likely a scam;
- If a website asks you to send your credit card number via email, do not do so. Only enter your credit card number on a website you trust;
- If the property requires you to submit a scan of your ID during the booking process, make sure this complies with the laws of the country you plan to visit;
- Make reservations using prepaid cards.
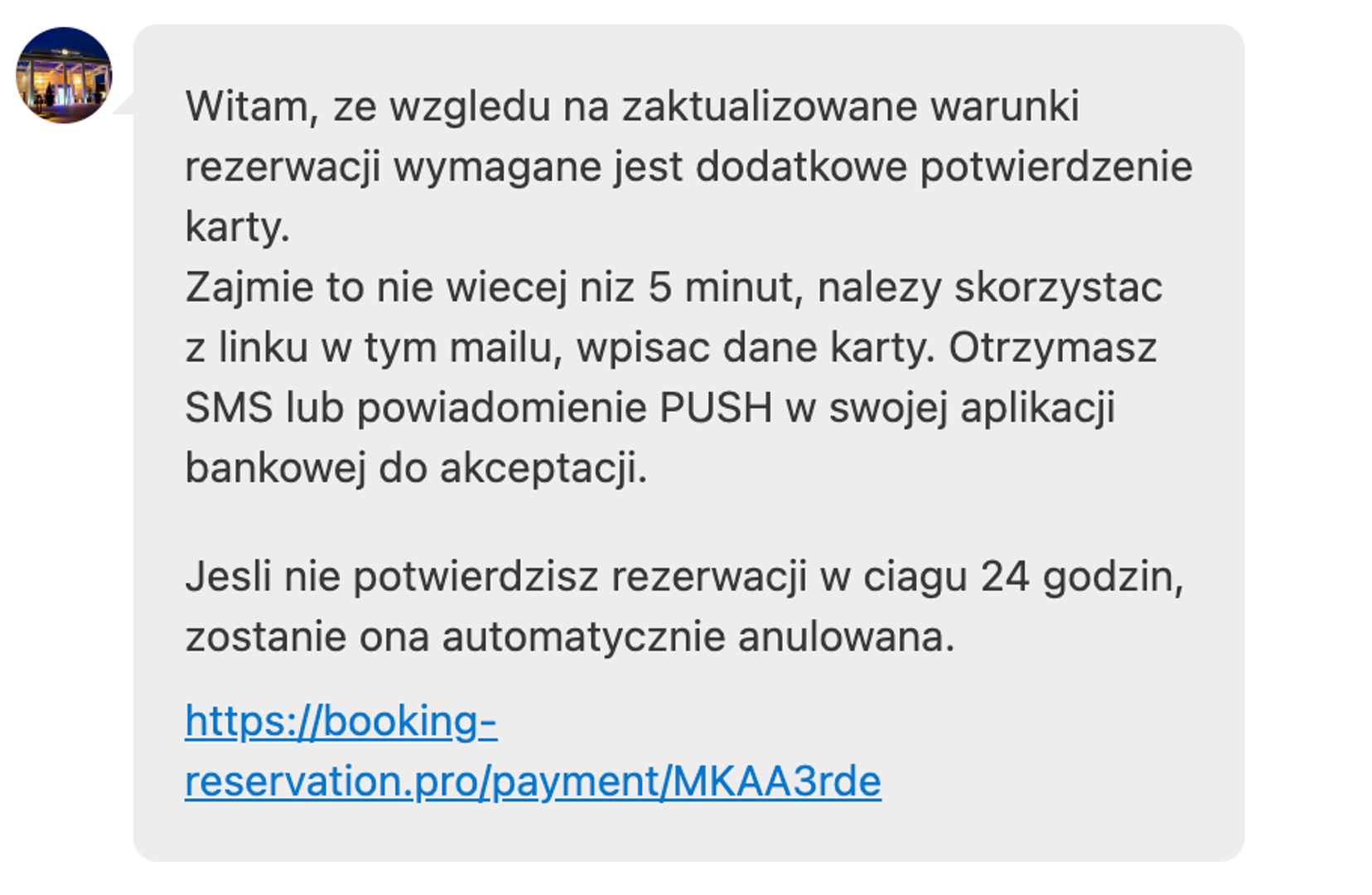
Any message or notification that suggests you need to act quickly—right now—should serve as a warning. “Urgent” messages and those urging you to take specific actions are designed to pressure you and try to trick you.
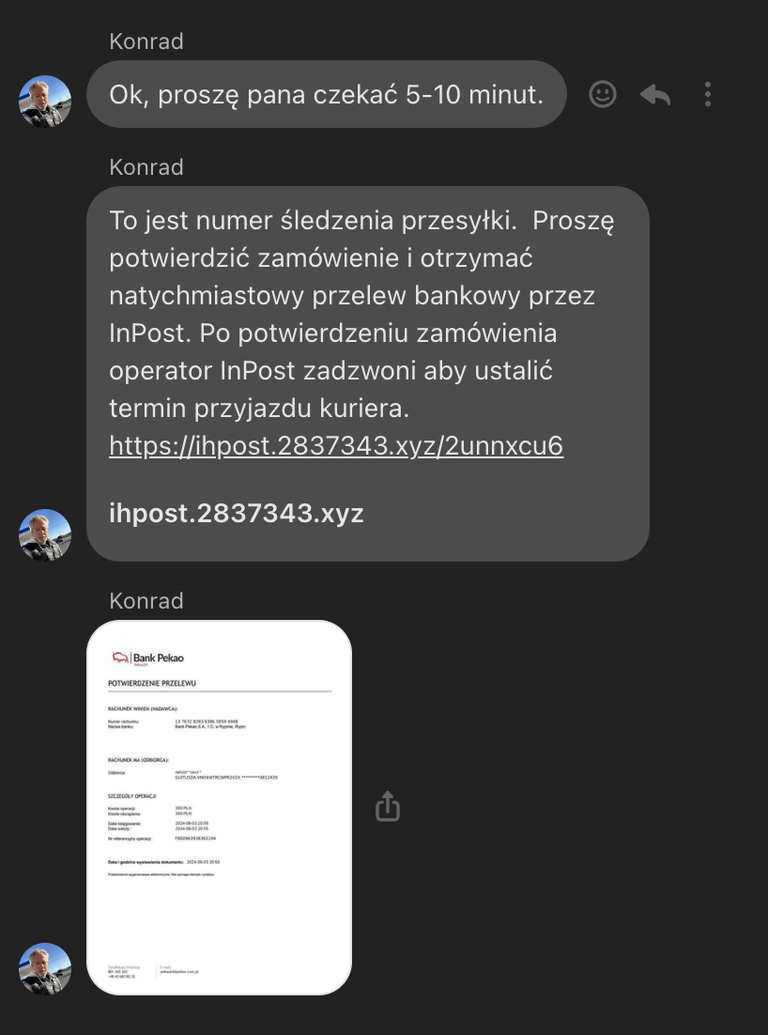
Attacks can occur even on large websites that offer accommodation bookings. The main reason for this is the use of weak passwords by these establishments. Cybercriminals log into the accounts of hotel and guesthouse owners and attempt to extort money from them.
Always make sure that any message you receive is from the hotel and not from criminals. If you’re unsure, call the hotel to confirm the message. You may also receive such messages via email or text message.
First and foremost, use your critical thinking skills!
Secure online payments
Cybercriminals want to make money off you and will try to do so using a variety of methods. The pre-vacation and vacation periods are prime times for them because of our increased online activity. In addition to booking accommodations, we also search for and purchase sports equipment, airline tickets, and tickets to concerts and other events. There’s really a lot of it!
When looking for such deals, we don’t just use websites; we also scour social media, where we can find products or services that interest us. The desire to snag that one-of-a-kind, best deal once again lowers our guard, leaving us vulnerable to the fake offers set up by scammers.
Criminals constantly use a variety of manipulative techniques—such as exceptionally attractive offers, low prices, and time pressure—to achieve their goals by impersonating others. Their creativity and use of advanced technologies, including artificial intelligence, make it increasingly difficult to detect their activities.
How do scammers try to take advantage of us?
- They create websites that mimic official stores and offer products at lower prices. These offers are available “today only”;
- The same things are popping up on social media;
- To make matters worse, cybercriminals promote their fake products and services through social media ads. They do this by using other people’s compromised accounts;
- Artificial intelligence helps them generate images of products that don’t actually exist, but which are appealing in terms of both appearance and price.
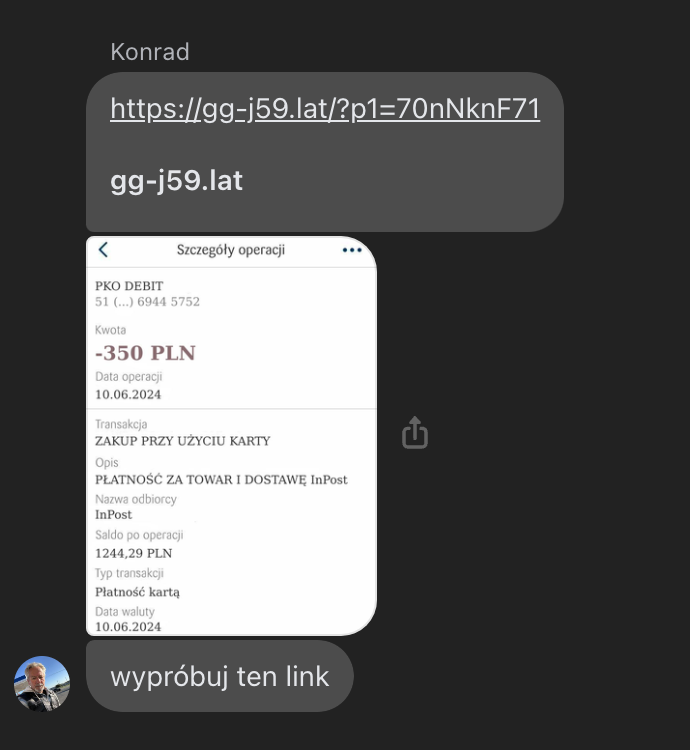
When criminals purchase a product from us, they pretend that the payment has been processed. They send fake websites and fabricated images suggesting that the transfer has been completed. In order to receive payment for the goods sold, we are required to enter our card details, bank login and password, or other sensitive personal information on such a website.
How can you avoid falling for this scam?
- Before entering your credit card information or making a payment, carefully check which website you’re using;
- Pay using one-time cards, prepaid cards, or digital wallets;
- Set a limit for online transactions, just as you would for card payments or ATM withdrawals;
- Avoid impulse buying, and don’t let yourself be rushed. If something seems suspicious, it probably is;
- When confirming a bank transfer, make sure the amount and recipient are correct;
- Do not share your PIN or CVV2/CVC2 code with anyone;
- Confirm every transfer or payment using the bank's app installed on your phone;
- If you're buying an item, read its description carefully. If it contains grammatical errors or is written in broken Polish, be on your guard.
Safe ATM withdrawals
In many places, you’ll need cash to buy souvenirs or small toys for your child. That’s when withdrawing money from an ATM comes to mind. Unfortunately, criminals are always on the lookout and will try to rob you. They use special devices attached to ATMs that read your card information.

That’s why it’s a good idea to make a withdrawal without using an ATM card. In Poland, the easiest way to do this is by using BLIK codes. That way, you don’t risk having your card details stolen, since you aren’t using the card itself.
Another good option is to make a payment using contactless payments. And speaking of contactless payments, the best option is to use a card linked to your cell phone.
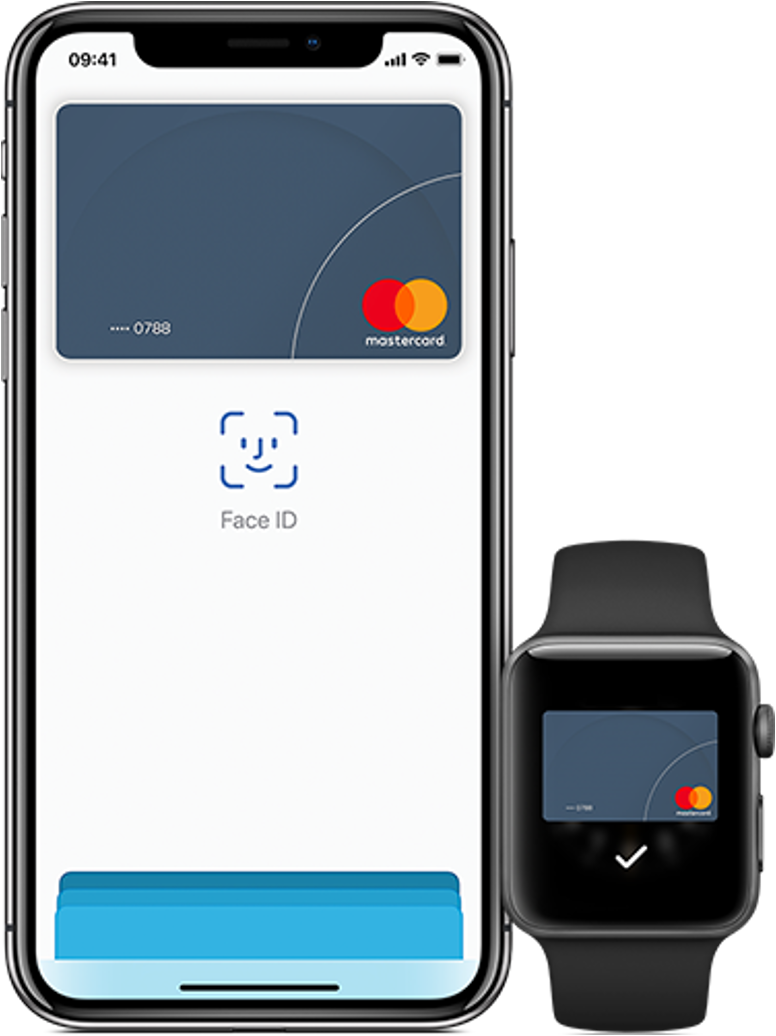
This is one of the safest payment methods. If your phone is stolen, no one will be able to make payments with it—because unlocking contactless payment features like Apple Pay or Google Pay requires the owner’s authentication, such as via Face ID. You can’t do that with a plastic card.
The phone itself doesn't store any data from the card, so there's nothing to steal.
Protection of identification documents
Identity theft is one of the most common crimes on the internet. Cybercriminals steal your identity and social media accounts and use them to commit further crimes. Identity theft can occur through online phishing (e.g., phishing for login credentials) or the theft of an identity document (e.g., a passport or ID card).
In this way, criminals try to create financial obligations, impersonate real accounts, and extort money from friends, or simply post compromising content on them.
When we think of identity theft, the first thing that comes to mind is the theft of an ID card or passport. When traveling within the country, it’s a good idea to have the mObywatel app on your phone, as it can perfectly replace a physical ID card in many situations.
When traveling abroad, always carry only the essential documents needed to prove your identity. Keep the rest of your documents in a safe place (such as a hotel safe), which can significantly reduce the risk of them being lost or stolen.
It is a very common practice to leave an ID as collateral, for example, when renting a car, water sports equipment, or ski gear. This is illegal! No rental company owner can require you to leave your ID. If necessary—for example, to pursue a claim—the rental business owner may record the information from your ID, which must be deleted once the service is completed.
If your ID is lost or stolen, be sure to report it as soon as possible. You can do this at a bank branch participating in the “Restricted Documents” program or online via the government website.
You can also use the Interbank Card Blocking System by calling +48828828828.
Also, be sure to report the loss or theft to the police, and once you’ve done so, keep a copy of the report.
Chargeback
Use your payment card whenever possible. Card transactions are covered by additional safeguards, such as chargebacks.
A chargeback is a reversal of a transaction designed to protect consumers from dishonest merchants, fraud, and payment system errors.
A chargeback allows you to recover your money even if the seller defrauds you by failing to deliver the goods or if the goods do not match the description. This also applies when the payment was made by someone other than the cardholder, such as when the payment card was stolen.
This procedure applies to both debit and credit cards, including Visa and Mastercard. To file a chargeback, contact your bank and request a chargeback form (not to be confused with a complaint form).
View related articles

Awarie IT zdarzają się każdemu
Od paru godzin trwa awaria komunikatora internetowego Slack. Kilka tygodni temu nie można było korzystać z usług firmy Google, a jeszcze wcześniej spora część Internetu nie działała z powodu awarii usług Cloudflare. Czy to możliwe, że usługi w chmurze są niedostępne?
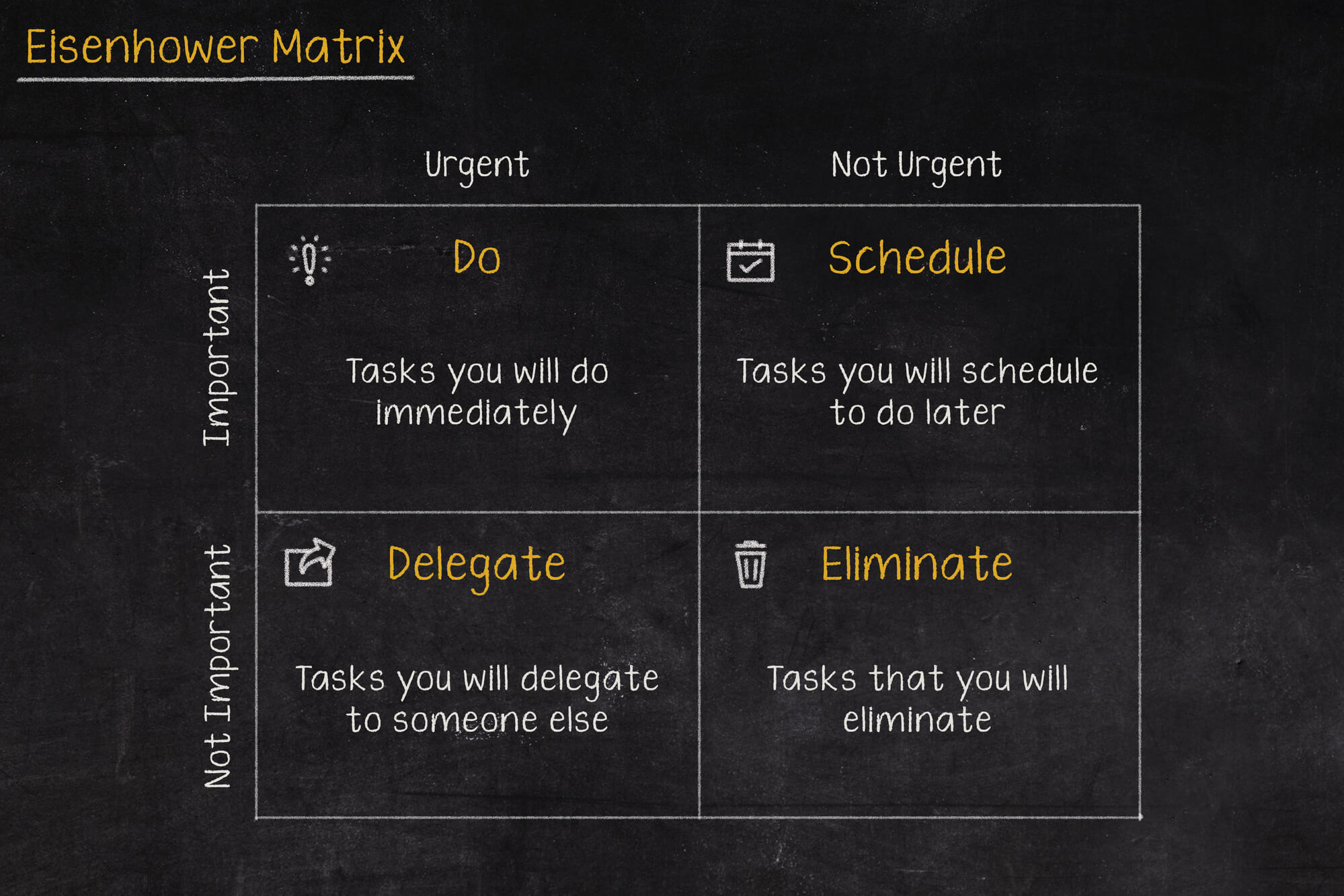
Macierz Eisenhovera, czyli jak zapanować nad priorytetami?
Iść na przerwę a może odpisać na tego maila, czy odebrać telefon od przełożonego? W jakiej kolejności zająć się tymi zadaniami, aby nie utracić nad tym kontroli i nie popaść w bezsilność? Rozwiązaniem tych problemów może być Macierz Eisenhowera (nazywana także Matrycą lub Kwadratem Eisenhowera).

Czy Alert RCB powinien informować o wyborach prezydenckich?
Komunikacja w niebezpieczeństwie jest jednym z ważniejszych zagadnień jakie się porusza podczas żeglowania, latania czy nurkowania. Ostrzeżenia potrafią uratować życie, dlatego nie powinny być lekceważone, a tym bardziej nie powinny swoją treścią prowadzić do ich zignorowania.