We lose your social security number, and you end up paying for surveillance
Oh my goodness! It’s happened again! After the huge ALAB scandal in 2023, which was supposed to be a wake-up call for the entire industry, we have another episode of the series titled: Your data is safe with us (until the weekend). This time, it was the Optimed network of medical laboratories. The result? Ms. Basia from Kętrzyn has just found out that her most intimate test results, her Social Security number, and her home address have become public property of hackers.
And the company? The company is generously handing out recommendations that will cost Ms. Basia not only a lot of stress, but also real time and money. Optimed kindly advises: block your Social Security number, pay for credit monitoring through BIK, and be on your guard with every phone call. In other words: we messed up, but now it’s up to you to worry and pay.
Déjà vu, the medical version
History tends to repeat itself, especially when customers—rather than company boards and the specific decision-makers who ignored warning signs for years—are the ones who pay for the mistakes. In November 2023, Poland was reportedly stunned by the news of a data breach at ALAB laboratories. Over 200,000 people ended up on the Darknet’s hit list. At the time, we were promised new standards, audits, and a government shield.
But the truth is that to this day, millions of Poles shrug their shoulders, claiming that it didn’t concern them because they never had tests done at a facility under the ALAB banner. This is precisely the moment when ignorance wins out in full force. These people don’t know that ALAB was a subcontractor for hundreds of smaller laboratories, clinics, and hospitals across the country. Their samples and data ended up there without their explicit knowledge, and then leaked online. Most people didn’t even check publicly available lists to see if their PESEL number had been put up for auction. They assumed that since they didn’t see the company’s logo on the door, they were safe. Today, in May 2026, we’re getting a repeat of the same lesson that no one wanted to learn, because why worry ahead of time?
Today, Optimed Medical Laboratories announced a security breach. A group of hackers—whether from the neighboring stairwell or the other side of the world (because what does it really matter?)—broke into the main database as if it were their own home. They stole whatever they wanted and that was that. What did they take? Everything needed to steal an identity: first names, last names, Social Security numbers, addresses, and—what hurts the most—lab test results.
What is Basia really at risk of?
Many experts and press spokespeople downplay the issue, referring to it as a data breach. For Basia, however, it marks the beginning of a horror story with several dark chapters:
-
Identity Theft 2.0: It’s not just the now-legendary loans and payday loans taken out in her name. It’s also the risk that someone will set up a shell company using her information, through which illicit funds will flow, and in two years, the tax office or the police will come knocking on her door.
-
Intimate blackmail: Medical data isn’t just ordinary database records. If Ms. Basia has been tested for sexually transmitted diseases, cancer, or hormonal disorders, hackers have a tool in their hands for years of blackmail. A message saying, “We know what you’re suffering from; pay 1,000 PLN or your family and neighbors will find out,” is a very real scenario.
-
The “expert doctor” scam: This is the most insidious form of phishing. Ms. Basia answers the phone. The voice on the line sounds professional: “Good morning, this is Dr. Kowalski from the specialist clinic. I’ve been analyzing your latest results from Optimed, and I have some bad news—your marker levels are critical.” If you do not immediately purchase our therapy for 2,000 PLN, the consequences will be irreversible. The scammer knows the test dates, specific parameters, and values. To the terrified patient, this sounds like a death sentence, and to the criminal, it’s easy pickings.
Ms. Basia and Her Costly “Good Advice”
Ms. Basia is not a hacker; she has no idea about SQL injection attacks, lack of input validation, or the fact that the company likely skimped on implementing a proper WAF (Web Application Firewall) that would filter out such attacks at the network perimeter. Ms. Basia just wanted to check her cholesterol level. Today she faces a dilemma: how is she supposed to change the data that was leaked?
In Optimed’s official statements, we read the standard corporate mantra:
To limit the potential consequences of the incident, we recommend immediately blocking your PESEL number via the obywatel.gov.pl website or the mObywatel app, as well as considering activating credit monitoring, e.g., through systems offered by the Credit Information Bureau. We also recommend exercising extreme caution regarding emails, text messages, and phone calls that may be an attempt to extract additional data.
This is the height of audacity. The company loses your data, and in return gives you... a list of tasks to complete in your free time. It is Ms. Basia who pays the real price for the corporation’s mistakes:
-
Money for monitoring: Why should Ms. Basia pay several dozen zlotys a year for monitoring through BIK just to check whether a hacker is taking out a loan in her name? The company recommends this expense because it was unable to protect her identity on its own.
-
Replacing documents: Since her Social Security number and address were leaked, Basia now has to run to a photographer, pay for photos, and wait in line at the government office just to replace her ID card—all for peace of mind. The company loses data, and you waste your morning battling bureaucracy and filling out new forms for a new ID card.
-
Time and nerves: Hours spent learning how to use mObywatel and tracking announcements. Every notification on your phone, every email, and every call from an unknown number is now a potential phishing attack. Basia has to become a digital detective because Optimed has failed as a guardian.
Great surprise after years of ignoring the issue
What’s most striking is that the scenario always plays out the same way, because many companies believe: “This doesn’t apply to us; we’re too small.” Management treats cybersecurity like a black hole where money disappears without yielding any reach or sales figures in return. Employee training? They already know how to use Word—why would they need to know about social engineering? System updates and regular patch management? If it works, don’t touch it, because the production environment might crash, and we don’t have the budget for staging and thorough testing.
Many employees simply couldn’t care less. To them, cybersecurity is an IT problem, not their daily responsibility. Sending passwords on sticky notes, clicking on every link labeled “promotion,” or sharing files without any security measures is a sad norm. Audits and professional penetration tests? After all, the IT guy who handles the toner says it’s safe because we have antivirus software on the computer at the front desk.
And then... the board is in for a huge surprise! Oh dear, we’ve fallen victim to an unprecedented, sophisticated attack! The truth is brutal: hackers often don’t need to be sophisticated. All they need is a vulnerable CMS system that hasn’t been updated in three years, a lack of network segmentation, and an employee who thinks security is just boring theory. Without a SIEM (Security Information and Event Management) or SOC (Security Operations Center) system in place, the company only finds out about the breach when hackers put the database up for sale.
The “14 Days to Forget” Strategy
The PR procedure in such cases is perfected to a tee in Poland.
-
Notify users (because the GDPR requires it).
-
Use a passive-aggressive apology (We were the victims of an attack – sounds more dignified than: we didn’t block access).
-
Post a message on the homepage (preferably in small print).
-
Wait 14 days until the media moves on to something else, then delete the message. We’ll pretend nothing happened.
In a month, this type of company will once again be a cheerful brand. The fact that Ms. Basia’s data will circulate online for hundreds of years won’t appear in their annual report. Digital data is immortal, unlike the patience of the deceived patients.
Fast cars, no drivers
Poland is undergoing record-breaking digitization. We have mObywatel, the mandatory KSeF collecting data on every transaction in the country, and chatbots in every government office. The problem is that as a country we’re handing out fast sports cars to everyone, but no one has taught us how to drive them.
We’re speeding down the highway of digitalization, forgetting that without seatbelts (cybersecurity) and brakes (real investments in IT infrastructure), every fender bender ends in tragedy. The person responsible for security in medical companies is still too often an IT specialist who deals with cables and toner, and management boards treat security as a cost rather than a foundation. We’re implementing systems like KSeF, which are a goldmine of information about Poles’ finances, but do we really know how to guard the keys to this treasure trove, or will it end as usual—with a huge surprise and another free lesson for hackers?
Punishment? Maybe someday...
Will the company pay? The head of the Personal Data Protection Office (UODO) may impose a fine. But history shows that corporate lawyers will fight it out in court for years until the case fades away. For the company, the fine is just a cost of doing business. For Basia, it means living in fear of every unknown phone number for the rest of her life.
Conclusions? As long as a medical data breach is treated as lightly as a broken coffee maker, nothing will change. Basia is left on her own with a restricted PESEL number, paid BIK credit monitoring, and a new ID card. And us? We’re waiting for the next leak. Because we changed our password, right? To May2026!
View related articles

Awarie IT zdarzają się każdemu
Od paru godzin trwa awaria komunikatora internetowego Slack. Kilka tygodni temu nie można było korzystać z usług firmy Google, a jeszcze wcześniej spora część Internetu nie działała z powodu awarii usług Cloudflare. Czy to możliwe, że usługi w chmurze są niedostępne?
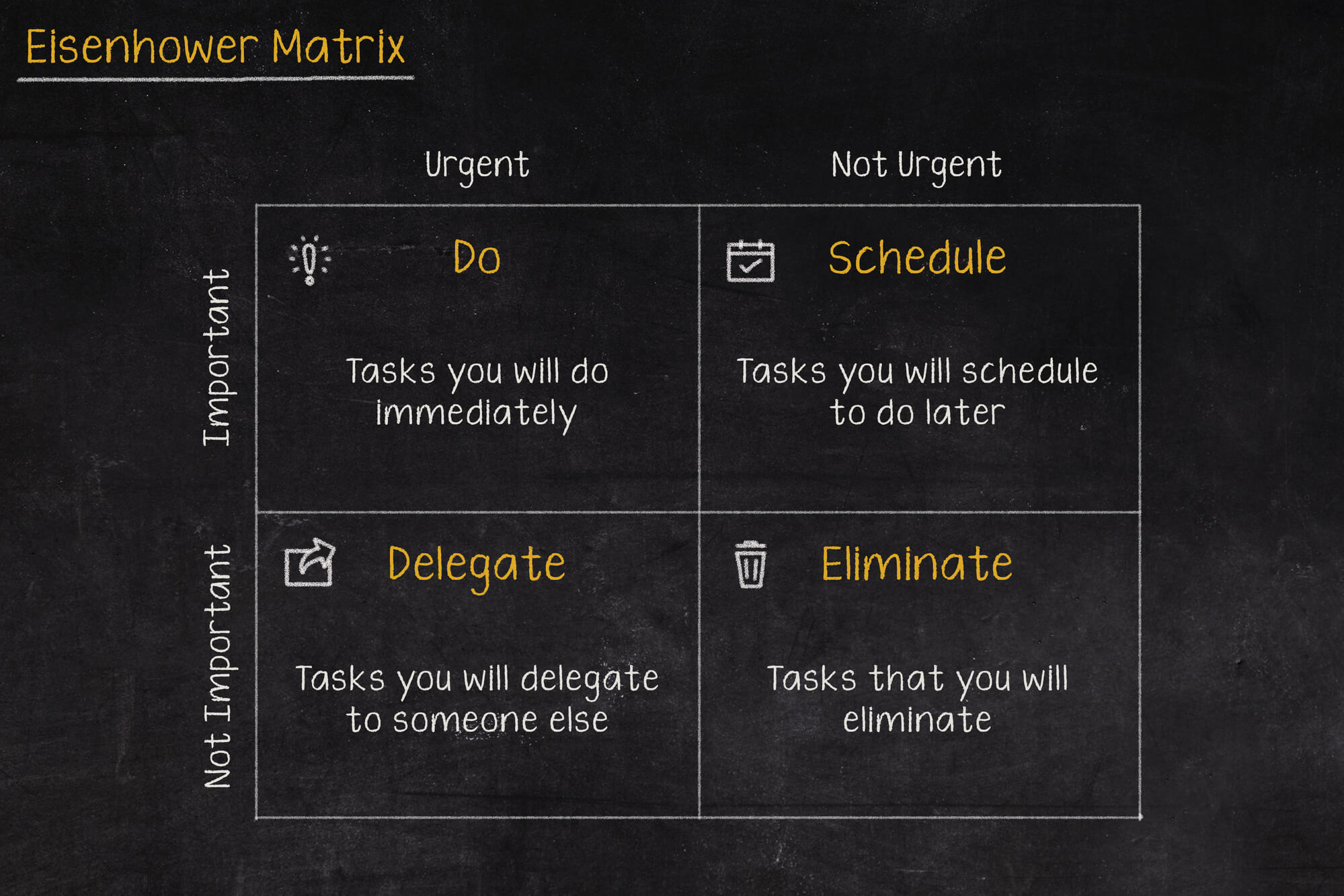
Macierz Eisenhovera, czyli jak zapanować nad priorytetami?
Iść na przerwę a może odpisać na tego maila, czy odebrać telefon od przełożonego? W jakiej kolejności zająć się tymi zadaniami, aby nie utracić nad tym kontroli i nie popaść w bezsilność? Rozwiązaniem tych problemów może być Macierz Eisenhowera (nazywana także Matrycą lub Kwadratem Eisenhowera).

Czy Alert RCB powinien informować o wyborach prezydenckich?
Komunikacja w niebezpieczeństwie jest jednym z ważniejszych zagadnień jakie się porusza podczas żeglowania, latania czy nurkowania. Ostrzeżenia potrafią uratować życie, dlatego nie powinny być lekceważone, a tym bardziej nie powinny swoją treścią prowadzić do ich zignorowania.