Who is watching you through your webcam?

Imagine this scenario: you install a modern camera in your living room to keep an eye on what your dog is doing while you're at work. Or you install surveillance in your spa or Pilates studio to keep an eye on the reception area and feel safer. You feel calm, you can view the feed on your phone, and technology is working for you.
Now imagine that at the same moment, someone on the other side of the world—or worse, your neighbor—is viewing the same image. And this isn't a scenario from the movie “Black Mirror” or some distant conspiracy theory. It's the reality for thousands of people who have unwittingly invited hackers into their bedrooms, offices, and even doctors' offices. Surveillance, which was supposed to give a sense of control, has become a window for criminals.
Table of Contents
Be afraid of the vacuum cleaner, not the laptop
Camera on your laptop covered? That's not the problem. Many of us instinctively cover the cameras on our laptops, fearing that hackers or corporations are tracking our every move via our computers or smartphones. The fear of ubiquitous surveillance through these personal devices is often exaggerated.
However, today, the real revolution in violating our privacy is not happening because of laptops, but because of Internet of Things (IoT) devices, which we enthusiastically welcome into our living rooms and backyards. Be more afraid of the camera in your vacuum cleaner than the one in your laptop.
A perfect example is the recent case of DJI's popular autonomous vacuum cleaners. The whole story began with an innocent experiment by a hacker who decided to see if he could control his cleaning equipment using a regular PlayStation controller.
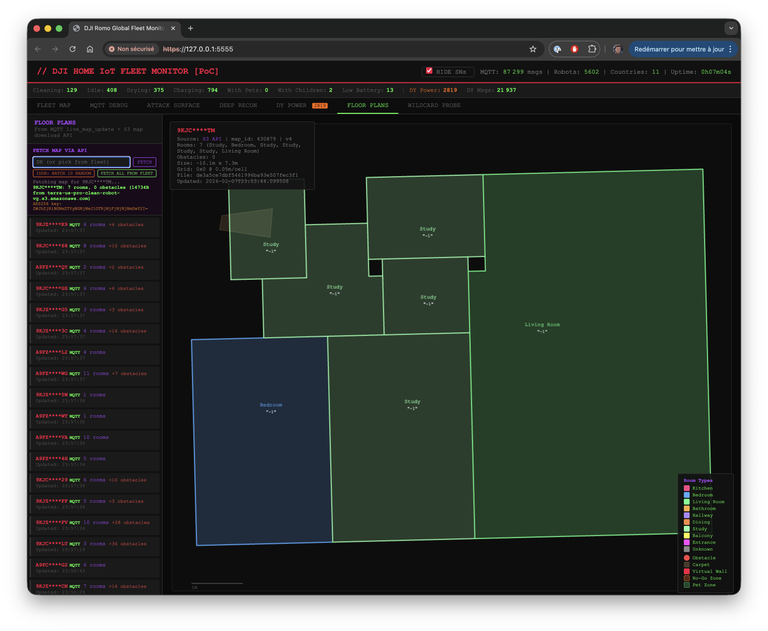
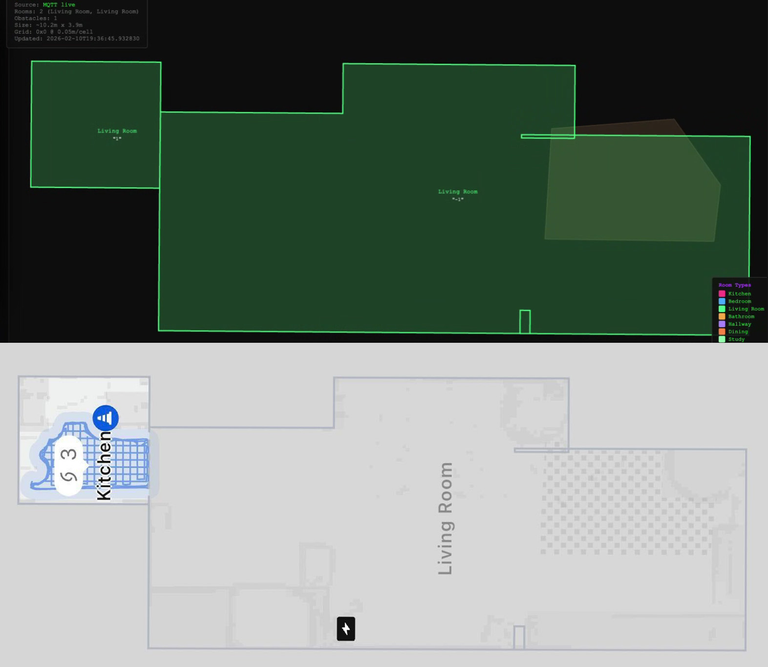
While analyzing how the robot communicates with the manufacturer's cloud, the researcher discovered a huge vulnerability. It turned out that although the devices connected to the home network were not directly visible from the internet, the company's intermediary server (an MQTT server used to send messages) remained completely unprotected.
The scale of the oversight proved terrifying. The hacker discovered that the access token generated for his vacuum cleaner also worked with other devices in more than 24 countries, giving him access to more than 6,000 cleaning robots around the world.
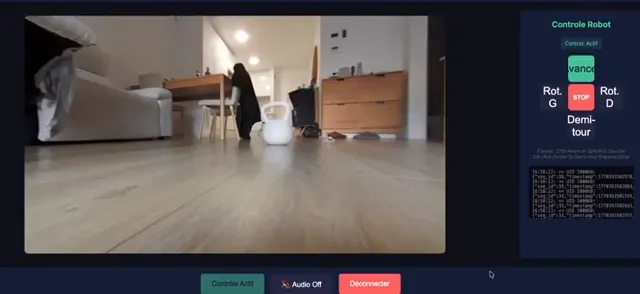
By connecting to a faulty server, an attacker could inject their own commands, exposing owners to a complete loss of privacy in their own homes. The vulnerability allowed remote control of the vacuum cleaner's movement, live viewing of the built-in camera, and eavesdropping on household members via the built-in microphone. What's more, the attacker could easily view and download detailed floor plans of the apartments, which the machine diligently mapped during its daily cleaning routine.
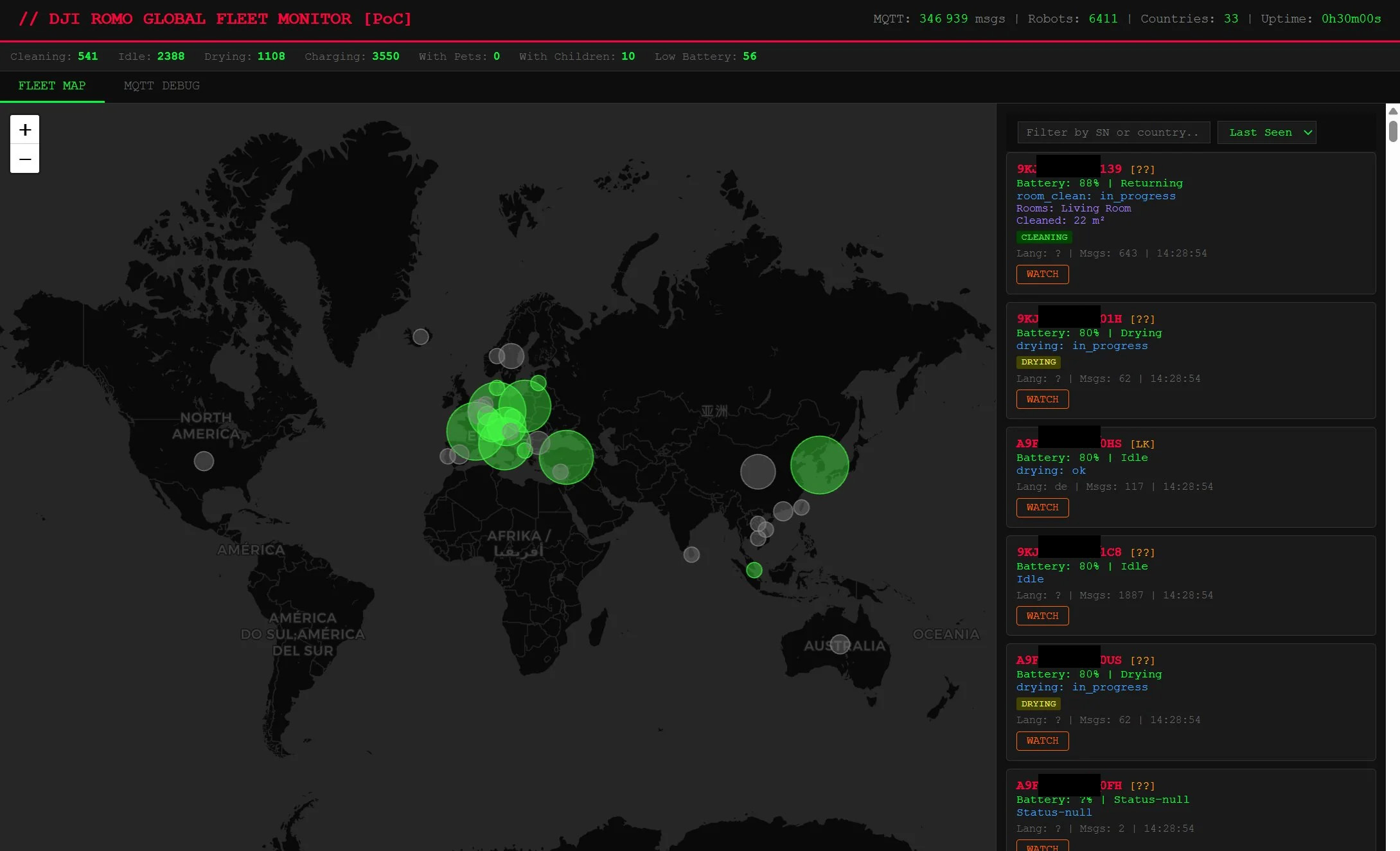
To prove the seriousness of the situation, the hacker even wrote a special application that allowed him to locate and take control of any vulnerable vacuum cleaner. The manufacturer eventually patched the vulnerability, although it took two iterations to release an effective fix. That's a very long time for such expensive equipment and a well-known brand.
Cheap webcams
We all like promotions. When we see a Wi-Fi camera for PLN 80 on a popular Chinese auction site, it's hard not to be tempted. The promise of HD images and access from an app for a fraction of the market price sounds great. The problem is that in the world of technology, “cheap” usually means “at the expense of your privacy and security.”
Manufacturers of budget equipment often cut corners on security programmers. As a result, you get a product that:
- It has buggy software: These cameras often have bugs that no one will ever fix. There is no budget for it. And that's it.
- It has hidden “backdoors”: These are intentional or accidental vulnerabilities that allow someone from outside—from the manufacturer to a random hacker—to access the image without your permission.
- Ignores data encryption: Your recordings travel over the internet to the manufacturer's servers and to your phone, but they are not encrypted. Anyone can see what you are doing in your home. There are even special websites where you can view such cameras.
Weak or missing passwords
Even the most advanced camera won't help if we leave the door open ourselves. The most common mistake made by non-technical people is leaving the default factory settings unchanged.
Think about it: after taking the camera out of the box, did you change the password to one that is at least 12-16 characters long and contains capital letters and symbols? If your password is admin123, 123456, polska1, or worse, you left it blank, it's like locking your house but leaving the key in the lock on the outside. Hackers don't sit around guessing passwords manually – they do it automatically. This way, in a matter of minutes, they can create a database of “live” views from homes around the world.
They hacked into 120,000 cameras.
However, the threat is not limited to advanced cleaning robots. To a large extent, it also applies to popular IP cameras, which we install in our homes and businesses on a daily basis to ensure our sense of security or to monitor pets and children. Just how illusory this sense of security can be is demonstrated by a terrifying case in South Korea, where the police recently arrested four suspects accused of hacking into private systems. Exploiting security vulnerabilities, the cybercriminals hacked into a total of over 120,000 surveillance devices. This gave the hackers remote access to images from cameras installed not only in private homes, but also in places requiring special discretion, such as karaoke rooms, Pilates studios, and even gynecological offices.
The consequences of this attack were dramatic for the privacy of the victims. The collected, often intimate recordings of the everyday lives of unsuspecting people were used to produce sexual material, which the perpetrators then successfully sold on a foreign website. The scale of the individual hackers' activities is staggering—although they operated independently of each other and did not form an organized group, just two of them were responsible for approximately 62 percent of all illegal recordings published on this portal over the past year. The record holder in this case took control of 70,000 cameras, while another perpetrator, with 63,000 cameras under surveillance, produced over 500 videos, earning the equivalent of several thousand dollars in cryptocurrency from their sale. This shocking case is a brutal reminder of the importance of cybersecurity.
Ring and the controversial “Search Party”
Even if you buy equipment from a giant like Amazon (owner of the Ring brand), you are not free from dilemmas. Their new Search Party feature sounds brilliant on paper: if your dog goes missing, the AI system searches through footage from all your neighbors' cameras in the area to find your lost pet.
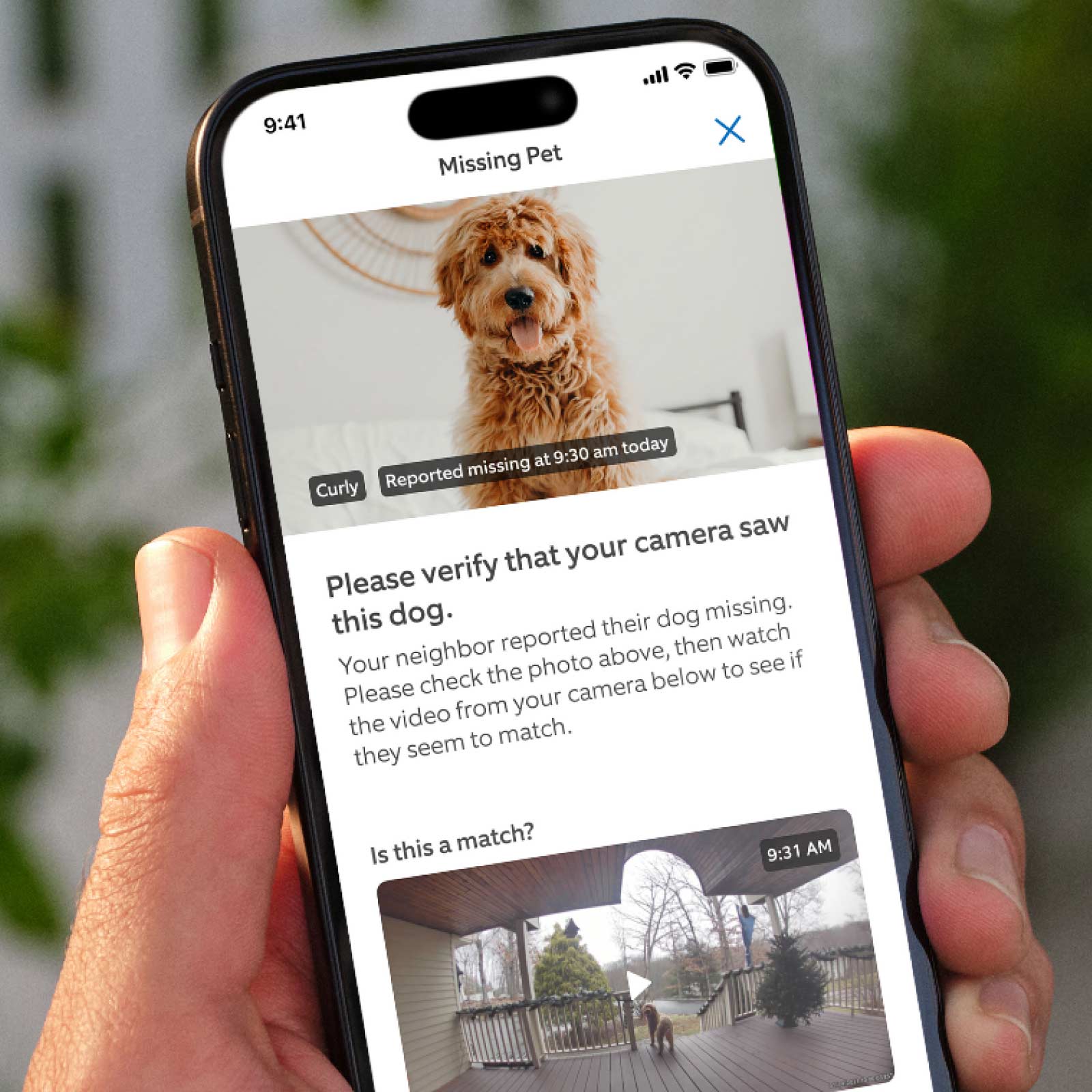
Sounds like a helping hand from the community, right? However, this “altruistic surveillance” is highly controversial:
- Function creep and mass surveillance: Systems created for a noble or specific purpose (e.g., Ring's “Search Party” feature, which uses artificial intelligence to connect neighbors' cameras to search for lost dogs) can become tools for mass surveillance. Leaked internal emails from Ring's CEO suggest that this technology is intended to be the foundation for broader “crime elimination,” raising concerns that in the future, cameras will be used to track people or vehicles across entire neighborhoods on a massive scale.
- Access to recordings by law enforcement and government agencies: The partnership between camera manufacturers (e.g., Ring) and the police and companies providing surveillance systems for state authorities (such as Axon and Flock Safety) is a cause for great concern. Even though some of these agreements have been withdrawn, law enforcement agencies have mechanisms to bypass users (e.g., warrants and subpoenas) or features such as “Community Requests,” raising concerns about the use of video by immigration services (ICE) and the creation of a police state.
- Lack of consent from passersby and risks associated with biometrics: Cameras that constantly analyze their surroundings using AI force the scanning of every passerby, mail carrier, or child within range of the lens who has never given their consent. The introduction of additional facial recognition features (“Familiar Faces”) risks violating strict biometric data privacy laws in many parts of the world.
- Default activation of tracking features (opt-out): Privacy advocates criticize manufacturers (especially Ring) for the fact that advanced community tracking features are often enabled by default as long as the user pays for a cloud subscription. Camera owners may unwittingly become part of a powerful surveillance network if they do not delve deep into the settings and manually disable the service.
- High percentage of AI errors (false positives): Camera systems are far from perfect. Artificial intelligence routinely flags animals, insects, shadows, or cobwebs as “person detected,” causing users to experience alarm fatigue. When such networks are used to search for criminals on a city-wide scale, false positives could lead to unnecessary police interventions.
- The trade-off between privacy and usability: To fully protect their recordings from companies and the government, users can enable “end-to-end encryption” (E2EE). However, this decision automatically disables the cameras' smart features (such as animal, face, or fire detection), as cloud-based algorithms cannot analyze encrypted video, forcing customers to choose between convenience and their right to privacy.
How to avoid being seen?
You don't have to throw your cameras in the trash. The key is to be a conscious user. Here's what you should do today:
-
Change your password immediately: This is an absolute priority. Use a unique, difficult password. It is best to use a password manager so you don't forget it.
-
Enable two-factor authentication (2FA): If your application offers this feature (e.g., SMS code or phone notification when logging in), be sure to enable it. It is the best defense against hackers who know your password.
-
Regular updates: If the app asks you to update the camera's firmware, do it immediately. This is how manufacturers patch holes that hackers could exploit.
-
Cover it when you don't need it: Sounds obvious? If you have a camera in your bedroom or bathroom, simply unplug it or physically cover the lens when you are at home. Your privacy is worth those few seconds of effort.
-
Be careful with the cloud: Check what happens to your recordings. Are they stored on the manufacturer's server? For how long? If possible, choose cameras that store data locally (e.g., on a memory card inside your home) rather than sending everything to the internet.
Remember, the camera in your home is there to protect you from thieves, not to become a tool that allows thieves to steal your privacy.
View related articles

Awarie IT zdarzają się każdemu
Od paru godzin trwa awaria komunikatora internetowego Slack. Kilka tygodni temu nie można było korzystać z usług firmy Google, a jeszcze wcześniej spora część Internetu nie działała z powodu awarii usług Cloudflare. Czy to możliwe, że usługi w chmurze są niedostępne?
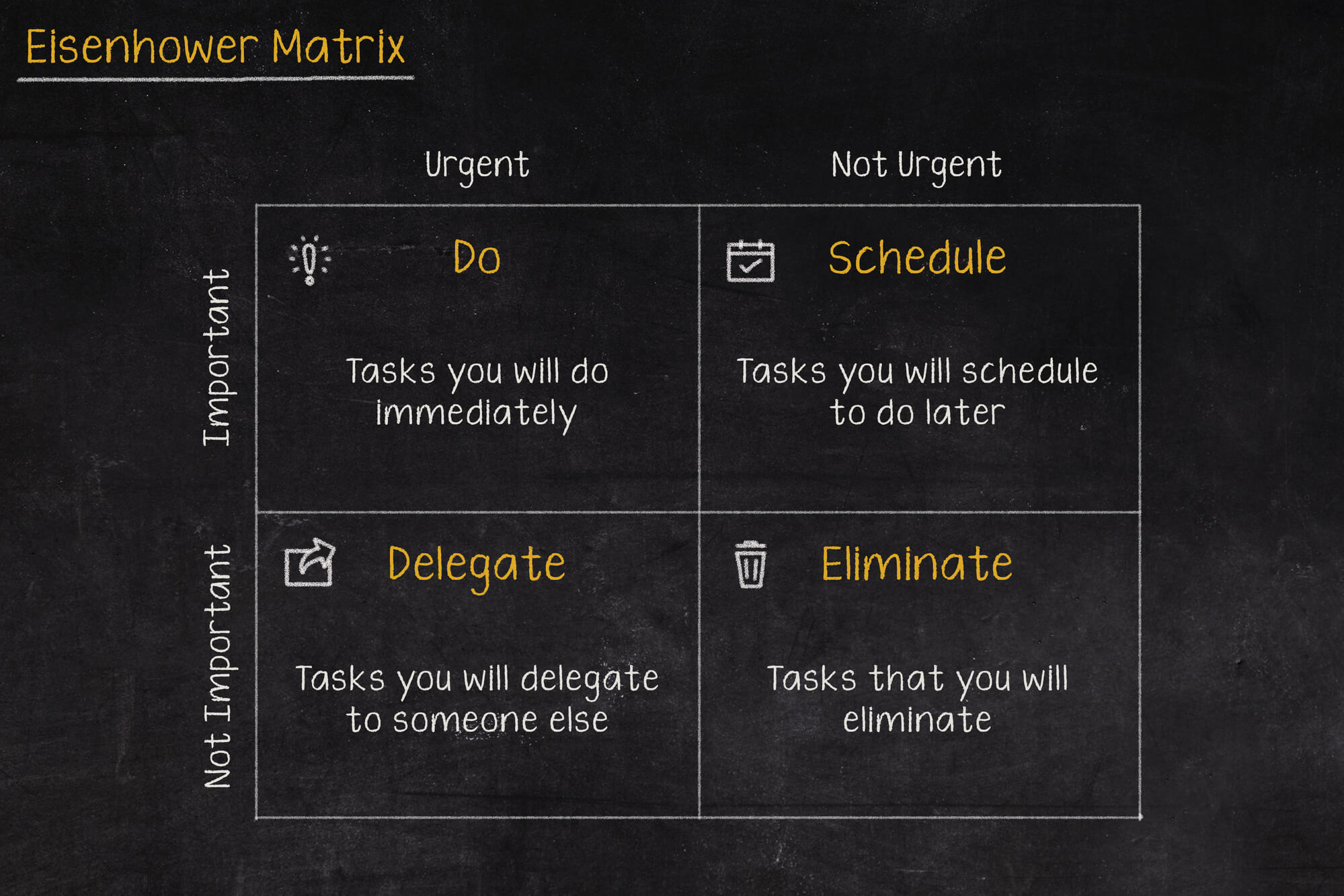
Macierz Eisenhovera, czyli jak zapanować nad priorytetami?
Iść na przerwę a może odpisać na tego maila, czy odebrać telefon od przełożonego? W jakiej kolejności zająć się tymi zadaniami, aby nie utracić nad tym kontroli i nie popaść w bezsilność? Rozwiązaniem tych problemów może być Macierz Eisenhowera (nazywana także Matrycą lub Kwadratem Eisenhowera).

Czy Alert RCB powinien informować o wyborach prezydenckich?
Komunikacja w niebezpieczeństwie jest jednym z ważniejszych zagadnień jakie się porusza podczas żeglowania, latania czy nurkowania. Ostrzeżenia potrafią uratować życie, dlatego nie powinny być lekceważone, a tym bardziej nie powinny swoją treścią prowadzić do ich zignorowania.